By Ritika Chakraborty, Second year, Computer Science
For years maths has been keeping our data safe, but with the latest quantum breakthroughs, this may no longer be the case.
Have you ever opened a new WhatsApp chat and wondered what on earth “end-to-end encryption” means? Or what it means for a connection to be “secure”? Encryption is the practice of turning plaintext into an encoded message in order to keep it safe from eavesdroppers, and cryptography is the study of this practice. Everything you do online is kept secure by our current encryption methods; from simple messages to financial transactions, none of it would be safe without encryption. Encryption works by generating secret keys, essentially mathematical passwords which lock and unlock your data, which are impossible to derive without solving the underlying maths problem. These problems famously involve factorising very large numbers, or discrete logarithms, which classical computers would take years to solve. Whilst for now this works just fine, there is an ever-looming threat to our current cybersecurity methods: quantum computers.
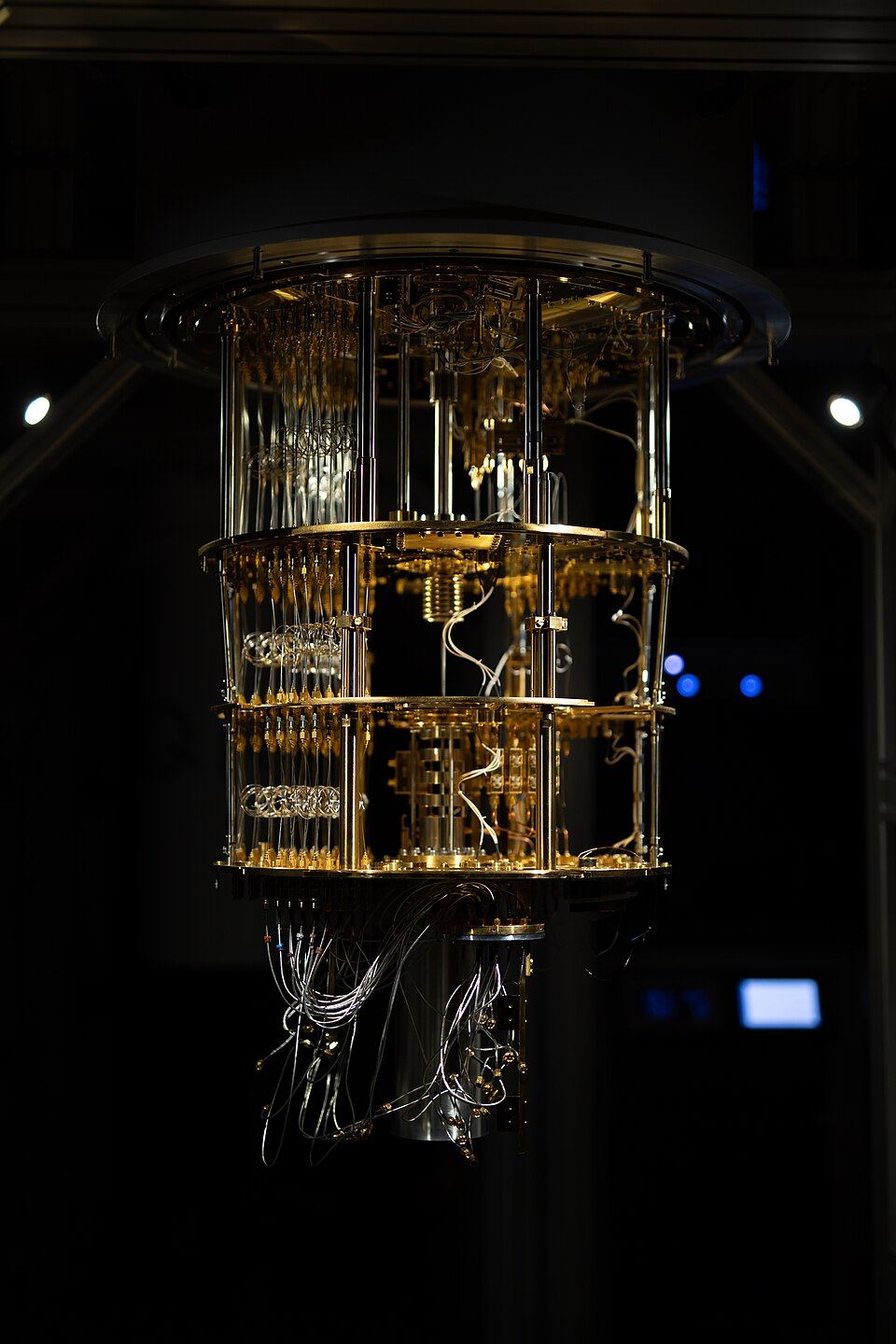
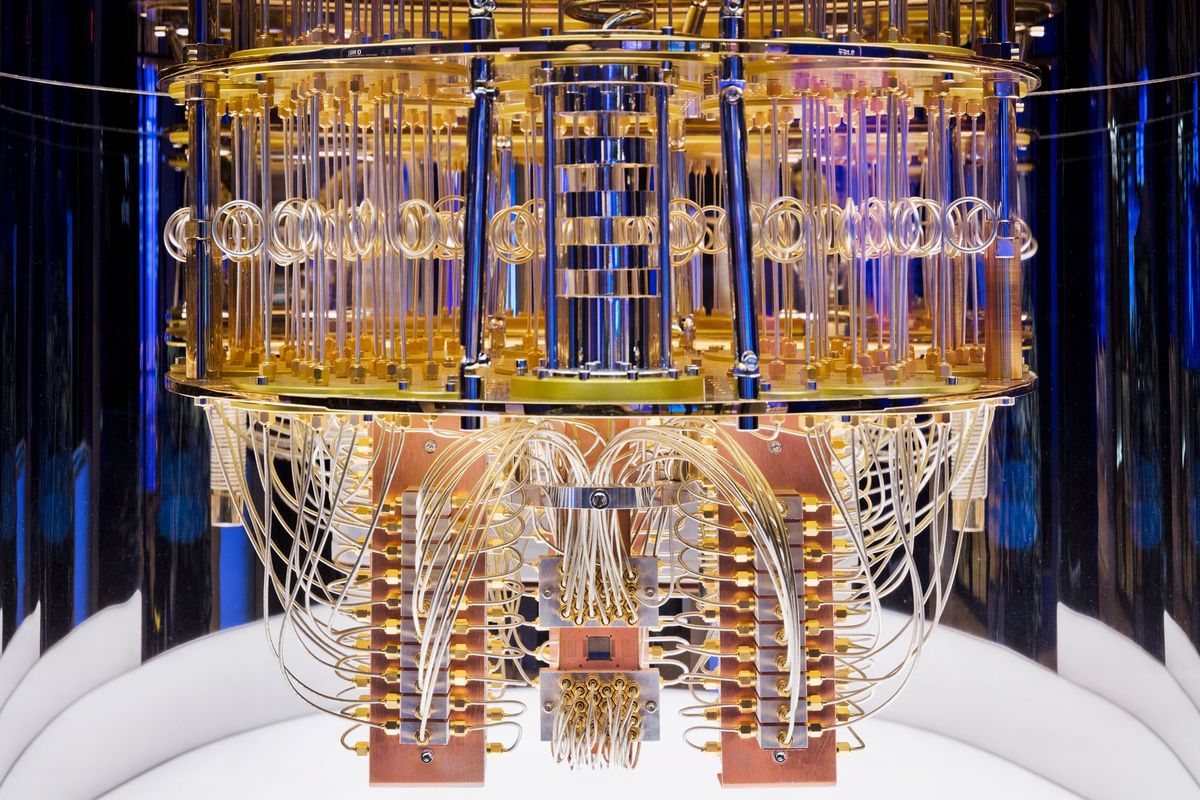
Quantum computing relies on two key quantum phenomena - superposition and entanglement. Classical computers store information as bits, which can only be either zero or one. Quantum computers however, store information as quantum bits - or qubits - which can use a property called superposition to exist as a blend of zero and one at the same time. We can then use these qubits to make registers, which become correlated with each other in a unique way - known as quantum entanglement. This combination of quantum superposition and quantum entanglement allows us to encode information in a very large number of states simultaneously, which is what makes quantum computers so special.
Classical encryption’s security rests entirely on the assumption that solving these specific maths problems with such large numbers takes an impossible amount of time, but this security falls apart in the face of quantum computers which, due to their ability to explore vast numbers of possibilities at once, reduce problems that would take classical computers thousands of years to ones solvable in seconds. The good news is, we’re in the Noisy Intermediate Scale Quantum (NISQ) era, meaning quantum computing is more of a proof-of-concept than a real thing. This is because qubits are extremely fragile and sensitive; they require extreme isolation or else they could cause errors in state and thus calculations. Most advanced systems at the moment use between 100-1000 qubits, most for error checking, whilst it’s estimated that thousands or even millions would be needed to carry out any cryptographically-relevant calculations.
So what happens when the NISQ era ends? Two distinct approaches are emerging to protect data from quantum threats: Post-Quantum Cryptography (PQC) and Quantum Cryptography. Whilst similar sounding, these are actually two entirely different concepts, with PQC taking a maths-based approach versus Quantum Cryptography’s physics-based.
PQC is simply an evolution of classical cryptography, still using maths problems to encode keys, but ones that quantum computers are no better at solving than classical ones. Whilst quantum computers can quickly sift through possible solutions to factorisation or discrete logarithm problems, certain other mathematical structures offer no shortcut, even to a quantum computer. In 2024, the National Institute of Standards and Technology (NIST) selected four algorithms to be standardised for PQC, three based on structured lattices and the fourth on hash functions, which some major platforms have already begun adopting.
Quantum Cryptography on the other hand, uses a physics-based approach to distribute keys, known as Quantum Key Distribution (QKD). Say you want to send an encrypted message to your friend - first you need to send them your key. To do this, you would encode random bits (zeroes or ones) onto photons by choosing one of four polarisations: vertical, horizontal, diagonal-left, or diagonal-right. You then send these photons, through a fibre-optic cable, to your friend. Upon receiving these photons, your friend randomly selects a basis for each photon and passes it through a corresponding beam-splitter. The crucial point here is that your friend has no idea which basis you used when you sent them the photons. Afterwards, you tell your friend which basis you chose, and they discard any photons where the bases didn’t match.
The remaining photons are the ones where you both chose the same basis, and the polarisation values of those make up your key. It’s worth noting that QKD only handles the distribution of the key itself; the actual message is still encrypted using classical methods. This prevents the key itself ever being directly transmitted, and due to the properties of quantum systems it makes this method entirely secure (in theory). There is no way to measure the state of a quantum system without altering it, so if someone was eavesdropping on your conversation, there would be a higher than expected error rate on your friend’s end, alerting you both to the hacker. Additionally, they would have no way of finding out which basis you used, leaving their intercepted information useless.
Whilst the threat of quantum computers is still some way off, the time to act is now; overhauling the cryptographic structure that underpins the entire internet is no easy feat, and won’t happen overnight. Cybercriminals are already believed to be harvesting encrypted data now, with the intention of decrypting it once cryptographically-relevant quantum computers arrive. Thankfully, the cryptographic community already saw this coming. NIST’s PQC standards are finalised, major platforms such as Signal and iMessage already support PQC, and governments and financial institutions worldwide are already deploying QKD networks.
So next time you see that WhatsApp pop-up or the padlock in your browser, it’s worth remembering the maths problems that have kept your data safe for decades (and how quantum computers will soon render them trivial). And whether their replacement, built on the fundamental laws of quantum physics, will be ready in time is one of the defining technical challenges of this generation.
Featured Image: Planet Volumes / Unsplash
What interests you the most about quantum computing?